Table of Contents >> Show >> Hide
- Why AI tool evaluation is different from ordinary software buying
- Start with use-case triage, not vendor hype
- What to evaluate before you sign
- Contract terms that matter most in AI deals
- Operational controls after the contract is signed
- Experience from the field: what companies learn the hard way
- Conclusion
Buying an AI tool used to be a little like buying office coffee: pick a vendor, sign a subscription, and hope nobody cries. Those days are over. Today, AI procurement is part software deal, part compliance review, part risk negotiation, and part “please tell me this chatbot won’t invent a refund policy at 2 a.m.” exercise.
If your company is evaluating generative AI, AI copilots, automated decision tools, AI analytics, or embedded AI features inside ordinary SaaS products, the legal and risk review cannot be bolted on at the end like a decorative spoiler. It has to be part of the buying process from day one. The reason is simple: AI tools can touch confidential information, personal data, intellectual property, employment decisions, regulated workflows, customer communications, and brand reputation all at once. That is a lot of ways for one cheerful product demo to become a very expensive lesson.
This guide explains how to evaluate AI tools before signing, what legal and operational risks deserve attention, and which contract terms matter most when you want innovation without inviting chaos into the building.
Why AI tool evaluation is different from ordinary software buying
Traditional software usually performs predictable tasks. AI systems do not always behave so neatly. They can generate new content, change outputs based on prompts, rely on third-party models, draw from changing training data, and improve or drift over time. That means your risk profile is not limited to uptime, data hosting, and user seats. You also need to think about hallucinations, biased outcomes, training rights, explainability, provenance, model changes, and whether the vendor’s contract was drafted by someone who really loves vague verbs.
In practical terms, evaluating AI tools means asking four basic questions:
1. What exactly will the tool do?
Is it drafting marketing copy, scoring job applicants, summarizing patient notes, reviewing contracts, answering customers, or helping engineers write code? The use case matters because the legal exposure changes with the task. A writing assistant used for internal brainstorming presents very different risk from an AI system used to make hiring, pricing, fraud, health, or eligibility decisions.
2. What data will go into it?
Will users input source code, customer records, deal documents, employee information, product roadmaps, regulated health data, financial information, or trade secrets? If the answer is yes, your diligence needs to focus on data rights, retention, security controls, subprocessors, cross-border access, and whether the vendor can use your data for model improvement or training.
3. What comes out of it?
Outputs can create their own problems. AI output may be wrong, incomplete, misleading, biased, or too similar to protected content. If users rely on output without review, the legal issue is not theoretical. It is operational.
4. Who is accountable when it breaks?
This is where many teams get squeamish. The vendor says the customer controls use. The customer says the vendor built the model. Everyone agrees “responsible AI” is important, and nobody wants to define who pays when the system causes harm. Your contract has to answer that question before the incident, not after it.
Start with use-case triage, not vendor hype
The smartest companies do not begin with a thousand-question diligence list. They begin by classifying the proposed use case. A simple internal drafting tool might be low to moderate risk. An AI hiring screener, biometric system, health workflow assistant, or automated customer-facing bot can quickly move into high-risk territory.
A practical triage framework looks like this:
Low risk: internal brainstorming, summarizing public information, formatting drafts, nonbinding research support.
Medium risk: internal document review, coding assistance, workflow recommendations, customer support drafts reviewed by humans.
High risk: employment decisions, healthcare use, finance, insurance, pricing, surveillance, identity verification, biometrics, legal advice, fully automated external communications, or any use involving sensitive personal data.
This risk tier should determine the depth of review, the contract protections you demand, and whether the tool can be deployed at all.
What to evaluate before you sign
Data rights and training rights
This is the first place experienced lawyers look, and for good reason. Many AI vendors want broad rights to customer inputs, prompts, outputs, telemetry, and feedback. Sometimes those rights are tucked into online terms with language broad enough to drive a truck through. You want the opposite.
Your contract should say, clearly and directly, that your data remains yours. It should limit the vendor’s rights to what is necessary to provide the service. If the vendor wants to use your data for model training, benchmarking, or product improvement, that should be separately negotiated, narrowly defined, and usually declined for sensitive use cases. An opt-out hidden in a settings panel is not a serious protection when confidential information is involved.
Privacy and regulated data
If personal data goes into the system, confirm the legal role of each party and the relevant privacy terms. Is the vendor acting as a service provider, processor, or independent business? Does it support deletion, access, correction, and retention requirements? Are subprocessors disclosed? Is data stored or accessed abroad? Are logs, prompts, and outputs retained? If the use case touches health, finance, education, children, or employment data, sector-specific rules may apply on top of general privacy obligations.
For healthcare uses, for example, a normal vendor addendum may not be enough. The parties may need a business associate agreement, AI-specific security controls, and sharper language around model training, retention, and audit support.
Security and confidentiality
Do not let the words “enterprise grade” hypnotize anyone. Ask how the tool is secured in real life. You want information about encryption, access controls, logging, segregation of customer environments, incident response, vulnerability management, and whether customer content is used to fine-tune shared models.
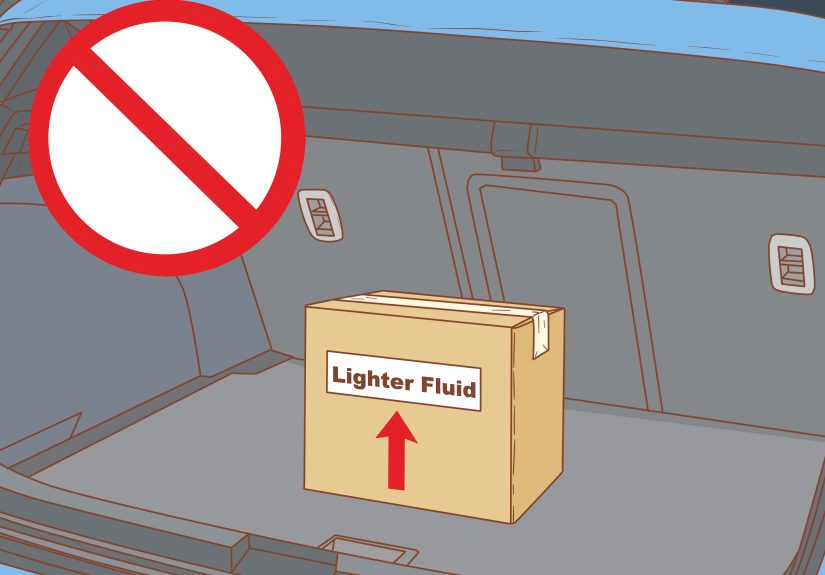
Also ask a boring but crucial question: what happens to prompts and outputs after the session ends? Many organizations focus on uploaded files while forgetting that prompts themselves can contain confidential strategy, deal terms, or source code. In AI deals, the prompt is often the secret sauce and the secret sauce should not leak.
Accuracy, testing, and human oversight
Vendors love saying their tool is “highly accurate.” That phrase is doing a heroic amount of work. Ask accurate compared to what, on which benchmarks, using which datasets, under what conditions, and with what failure rate? A demo showing perfect answers to easy questions proves almost nothing.
For meaningful diligence, request documentation on testing methodology, known limitations, high-risk failure modes, red-team results, and whether the system performs differently across user groups or contexts. If the tool influences consequential decisions, require human review and create rules for when humans can override or must verify output.
Bias and discrimination risk
If the AI tool touches hiring, performance, housing, lending, healthcare access, pricing, fraud screening, identity verification, or customer treatment, bias review is not optional. Existing discrimination and consumer protection laws do not disappear because a model made the recommendation instead of a manager in loafers.
Ask whether the vendor has tested for disparate impact, accessibility issues, and performance variation across populations. Require transparency about the intended use, prohibited use, and known limitations. If the system is not designed for high-stakes decisions, your internal policy should say so in plain English.
Intellectual property and output ownership
AI contracts can get slippery around ownership. Some vendors claim broad rights in outputs, especially if the output reflects model behavior or system-generated suggestions. Others say the customer owns outputs but then reserve rights to use similar content for service improvement. That is not the same thing as clean ownership.
You want contract language that addresses three separate issues: ownership of inputs, rights in outputs, and the vendor’s rights to underlying models and tools. If your team is generating marketing assets, software code, product content, or legal drafts, clarify what rights you receive and whether the vendor offers any IP indemnity for third-party claims tied to the service or its training materials.
There is also a practical point here: even when outputs are usable, not every AI-generated result will qualify for copyright protection without meaningful human contribution. Companies should not assume all output is automatically protectable just because someone typed a very passionate prompt.
Open-source and third-party dependencies
Many AI products rely on foundation models, open-source components, vector databases, speech engines, or third-party moderation tools. That is normal. What matters is transparency. Ask the vendor to disclose material third-party components and any restrictions that may affect your use, security, export controls, or licensing posture. Your company cannot manage risk you are not allowed to see.
Contract terms that matter most in AI deals
Scope of permitted use
The contract should define the approved use case. If the tool is being licensed for internal drafting support, do not let users quietly expand it into fully automated customer decisions. This protects both compliance and common sense.
Representations and warranties
Ask for specific promises, not fluffy adjectives. The vendor should represent that it has the rights needed to provide the service, that it will comply with applicable laws, and that it will not knowingly use your data beyond the agreed scope. For sensitive use cases, you may also want warranties around security practices, data segregation, and disclosure of material model changes.
Service levels and performance standards
Regular SaaS uptime commitments are not enough when the value of the tool depends on output quality, support responsiveness, and change management. Define service levels for availability, support, incident notification, and, where appropriate, measurable quality commitments. If a model update materially changes performance, your company should get notice and a remedy.
Indemnities
This is where negotiations get lively. Buyers often seek vendor indemnities for IP claims, data breaches caused by vendor failures, and certain legal violations tied to the service. Vendors often push back, especially on output-related claims. The realistic goal is not perfection. It is allocating the risks the vendor is best positioned to control.
If the vendor controls the model, training stack, hosted environment, and security architecture, it should not act shocked when asked to stand behind those things. A dramatic sigh is not a substitute for indemnity language.
Liability caps and carve-outs
Many standard contracts cap liability at a small multiple of fees. That may be wildly inadequate if the AI tool handles sensitive data or supports business-critical functions. Consider higher caps or separate caps for confidentiality breaches, data protection obligations, IP infringement, and gross negligence or willful misconduct.
Audit rights and documentation support
You do not need the right to camp in the vendor’s lobby with a clipboard. But you do need enough information to assess compliance. That may include security reports, audit summaries, penetration test attestations, subprocessor updates, records of material incidents, and cooperation with regulatory inquiries.
Change management
AI products evolve fast. That is exciting until the vendor swaps a model, changes retention settings, updates content moderation logic, or broadens training rights through a revised online policy. Require notice for material changes, a right to object in defined cases, and a termination right if the changes materially increase risk.
Exit, deletion, and portability
When the relationship ends, what happens to prompts, fine-tuned models, embeddings, output history, logs, and uploaded data? Your contract should address return or export rights, secure deletion, deletion timing, backup handling, and post-termination survival of confidentiality obligations. An elegant exit clause is much cheaper than a panicked email chain.
Operational controls after the contract is signed
Signing the contract is not the finish line. It is the starting pistol. Organizations need internal controls to govern approved AI use, employee training, prompt hygiene, review requirements, escalation paths, and prohibited uses. Keep a record of where AI tools are deployed, what data they touch, what decisions they influence, and who owns the ongoing review.
In other words, do not buy an AI tool on Monday and discover on Thursday that sales, HR, legal, and customer support are all using it differently with no rules. That is not innovation. That is group improvisation with regulatory consequences.
Experience from the field: what companies learn the hard way
In real-world AI contracting, the biggest mistakes usually do not come from wildly futuristic problems. They come from ordinary shortcuts. Teams fall in love with the demo, assume the enterprise version fixes everything, and treat legal review like a ceremonial speed bump. Then the details show up.
One common lesson is that procurement teams often underestimate how many AI vendors rely on layered third parties. The “vendor” may actually be wrapping someone else’s foundation model, someone else’s speech engine, someone else’s moderation tool, and a stack of open-source components held together by optimism and a product roadmap. None of that is inherently bad, but it means diligence has to go beyond the shiny front-end brand. Companies that ask only whether the vendor is secure usually miss the better question: secure compared to which dependencies, with what monitoring, and with what contractual backstops if one of those dependencies changes?
Another lesson is that data-use language matters more than sales conversations. A vendor representative may cheerfully promise that customer data is never used for training, but the contract may reserve rights to use service data, feedback, usage information, and de-identified content for broad product improvement. If the definitions are loose enough, the practical protection may be weaker than the customer thinks. Experienced buyers learn to distrust summary assurances and read the definitions section like it owes them money.
Companies also learn that AI output risk is often a workflow problem disguised as a technology problem. The model may be imperfect, but the real danger arises when employees treat output as authoritative, paste it into a client email, or route it into a high-stakes process without review. The most effective risk controls are frequently operational: clear approved uses, mandatory human review for important decisions, logging, escalation rules, and training that explains not just how to use the tool, but when not to use it.
There is also a subtle contract lesson that shows up again and again: standard clickwrap terms are usually written for scale, not nuance. They tend to favor unilateral updates, broad disclaimers, limited support commitments, and generous vendor rights around data and telemetry. Mature buyers push for a negotiated enterprise agreement because AI tools are rarely “just another app.” When the tool touches confidential business strategy, customer communications, code, health data, or employment workflows, the gap between clickwrap and negotiated paper becomes the gap between manageable risk and a future internal investigation.
Finally, companies learn that AI governance succeeds when ownership is clear. Someone has to own the use-case review. Someone has to approve the contract language. Someone has to monitor changes after deployment. Without that accountability, AI adoption becomes a scattered collection of well-meaning experiments. With it, organizations can move fast, capture value, and avoid the especially painful experience of explaining to executives why a “productivity tool” became a privacy, IP, bias, and incident-response project overnight.
Conclusion
Evaluating and contracting for AI tools is no longer a niche legal exercise for tech companies with large innovation budgets. It is a mainstream business discipline. The organizations that do it well are not anti-AI. They are anti-surprise. They define the use case, classify the risk, test the vendor’s claims, negotiate data and liability terms that match the real exposure, and build operational controls that keep the tool inside the lines.
If you remember one principle, make it this: do not buy AI like ordinary software. Buy it like a system that can influence decisions, generate content, touch sensitive data, and evolve after deployment. Because that is exactly what it is. And in contracting, clarity beats excitement every time.