Table of Contents >> Show >> Hide
- Why You Should Not Simply Turn Off Endpoint Protection
- 8 Safe and Simple Ways to Handle McAfee Endpoint Security Issues
- 1. Confirm Whether the Action Is Actually Necessary
- 2. Check for Notifications, Logs, or Quarantine Events
- 3. Ask for a Temporary Exception Through Official Channels
- 4. Schedule the Work During a Maintenance Window
- 5. Use a Test Machine or Isolated Environment
- 6. Verify the Software Source and Integrity
- 7. Update the Application, Definitions, and Policies
- 8. Escalate With Specific Business Context
- Common Situations Where Users Run Into Trouble
- Best Practices for IT Teams and Security Admins
- Final Thoughts
- Experience-Based Insights: What This Feels Like in Real Life
- SEO Tags
Let’s be honest: security software and productivity sometimes act like two roommates fighting over the thermostat. One wants everything locked down, the other just wants to open a file, install a tool, or run a script before lunch. If you use McAfee Endpoint Security in a business, school, or managed IT environment, you may occasionally feel tempted to shut it off and move on. That urge is understandable. It is also usually the wrong move.
In most organizations, McAfee Endpoint Security is centrally managed for a reason. It protects devices against malware, suspicious behavior, unsafe web activity, and a long list of digital headaches nobody wants. So instead of looking for risky shortcuts, the smarter path is to use safe, approved methods that solve the problem without breaking policy, triggering alerts, or making your device the office cautionary tale.
This guide walks through eight practical, admin-friendly ways to handle McAfee Endpoint Security when it gets in the way of legitimate work. You will also find real-world examples, troubleshooting ideas, and a longer experience-based section at the end to make the topic more relatable and useful for readers who have been there.
Why You Should Not Simply Turn Off Endpoint Protection
Endpoint security in corporate environments is not just “another app.” It is part of a broader security stack that may include centralized policy management, auditing, threat detection, incident response, and compliance controls. In many cases, users cannot disable it at all because the settings are locked by IT administrators. Even when a local option appears available, using it without approval can create business risk, violate policy, or leave the system exposed during a critical moment.
That matters because the times when people most want to disable protection are exactly the times attackers would love to exploit: software installs, macro-enabled files, admin tasks, external devices, and new development tools. In other words, the “quick workaround” often lands right in the danger zone.
The good news is that you usually do have options. They just look more like smart process and less like dramatic button-smashing.
8 Safe and Simple Ways to Handle McAfee Endpoint Security Issues
1. Confirm Whether the Action Is Actually Necessary
Before you blame McAfee Endpoint Security for ruining your day, confirm that it is truly the cause of the problem. Plenty of issues that seem security-related are actually tied to permissions, outdated software, missing dependencies, network restrictions, certificate errors, or application bugs.
A good first move is to document what you are trying to do, what error message appears, and whether the issue happens on one device or several. If the same installer works on a test machine but fails on your managed laptop, security policy may be involved. If it fails everywhere, the problem may live elsewhere. This five-minute check can save an hour of dramatic but unhelpful troubleshooting.
2. Check for Notifications, Logs, or Quarantine Events
Security tools often leave clues. If a file was blocked, quarantined, or flagged as suspicious, there may be a visible alert, dashboard message, or event log entry. Instead of guessing, look for the exact file path, rule name, or detection category. That information gives IT or security staff something real to work with.
Think of it this way: “My app won’t run” is a complaint. “The executable in this folder appears to be blocked after a reputation scan” is a useful report. One gets sympathy. The other gets results.
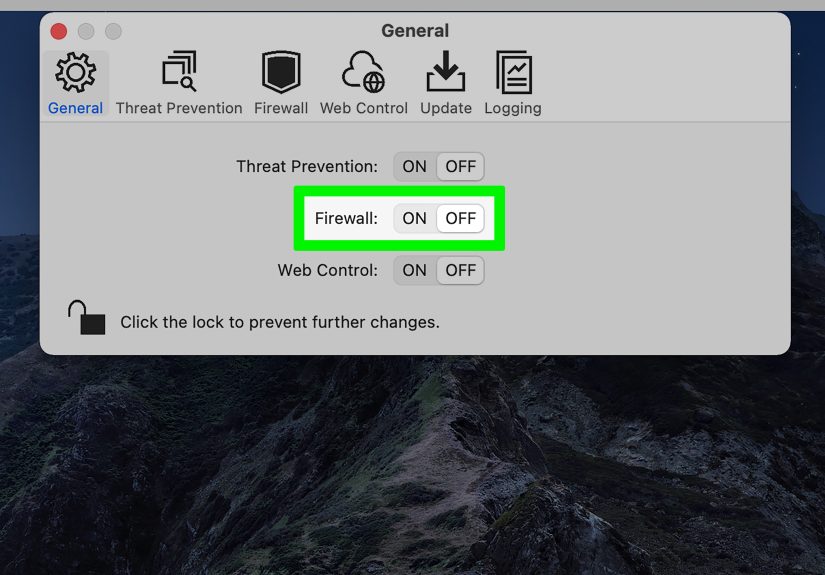
3. Ask for a Temporary Exception Through Official Channels
If a legitimate business tool is being blocked, the safest route is usually a temporary exception approved by IT or security. This may involve allowing a specific file hash, certificate, folder, process, or web destination, depending on company policy. The important part is that the change is reviewed, documented, and limited in scope.
Temporary exceptions are far safer than trying to shut off protection broadly. They solve the business problem while keeping the rest of the machine protected. In a healthy IT environment, this is standard practice, not a favor whispered across a cubicle wall like a spy movie.
4. Schedule the Work During a Maintenance Window
Some actions are better performed during a planned maintenance period. Large software deployments, driver changes, system migrations, and developer tool installations can behave differently under strict security controls. Rather than forcing the issue during a busy workday, ask whether the task can be scheduled during an approved maintenance window with IT oversight.
This approach is especially useful for servers, shared workstations, or regulated environments where every change needs to be traceable. It reduces risk, gives the support team time to prepare, and prevents the classic “I changed one thing and now six departments are unhappy” scenario.
5. Use a Test Machine or Isolated Environment
If you need to evaluate software, open suspicious-looking files from a trusted vendor, or test scripts that might trigger protection rules, use an isolated lab device, virtual machine, or sandbox approved by your organization. This allows legitimate testing without weakening protection on a production endpoint.
For developers, analysts, and IT staff, isolated environments are often the best compromise between security and flexibility. They let you experiment, validate behavior, and gather evidence for a policy adjustment request. They also dramatically reduce the chance that a normal workstation becomes the star of next week’s incident report.
6. Verify the Software Source and Integrity
Sometimes security products block a file because the file genuinely looks risky. That does not always mean it is malicious, but it does mean you should verify the source before asking anyone to allow it. Make sure the software comes from the official vendor, matches the expected version, and has not been repackaged by a questionable third-party site with all the digital charm of a back-alley trench coat sale.
If available, gather version details, vendor documentation, release notes, and any relevant business purpose for the software. The more context you provide, the easier it is for security teams to evaluate the request and respond quickly.
7. Update the Application, Definitions, and Policies
Compatibility problems can happen when the operating system, the application, or the endpoint security platform is out of date. Before assuming policy is the enemy, check whether the blocked app has a newer version, whether your system is behind on patches, or whether the security tool itself has pending updates managed by IT.
Organizations often tune endpoint policies over time to reduce false positives and improve compatibility. A problem that happened last month may already have a fix, a new exception, or a revised policy available. In other words, the solution may not be “turn it off.” It may be “let the grown-up software finish updating.”
8. Escalate With Specific Business Context
When all else fails, escalate the issue clearly and professionally. Explain what you are trying to accomplish, why it matters, what file or action is involved, what McAfee Endpoint Security appears to be doing, and what deadline or business impact is at stake. Good escalation is not complaining louder. It is making the case better.
For example, “Please review the block on this accounting tool installer needed for quarter-end processing” is far more effective than “Security is broken again.” One invites resolution. The other invites a deep sigh from a help desk technician who has already lived through enough.
Common Situations Where Users Run Into Trouble
Software Installation
New applications, plug-ins, command-line tools, and unsigned utilities are common triggers. Users often assume the installer is harmless because it came from a familiar vendor, but endpoint protection may still inspect behavior, reputation, or script activity before allowing it to run.
Development and Scripting
Developers working with local servers, package managers, scripts, or automation tools may encounter blocks more often than general office users. These cases often benefit from approved development environments, code-signing practices, and narrowly scoped policy exceptions.
Macro-Enabled Files or Downloaded Attachments
Files received through email, shared storage, or collaboration platforms may be restricted if they contain macros, executables, or suspicious patterns. The safest response is not to force them open. It is to validate the file and ask for review when the business need is legitimate.
USB Devices and External Media
Some environments also pair endpoint security with device control rules. If a removable drive or external device is limited, that may be part of a deliberate policy rather than a broken setting. Again, this is a job for approved access, not improvisation.
Best Practices for IT Teams and Security Admins
If your audience includes administrators, this topic is a reminder that users usually do not want to fight security for fun. They want to finish their work. When false positives, unclear alerts, or slow exception workflows get in the way, people start hunting for unsafe shortcuts. That is a process problem as much as a technology problem.
Clear request paths, readable alerts, documented exception criteria, and fast turnaround on legitimate cases can reduce friction dramatically. Security that feels reasonable tends to be respected. Security that feels random tends to inspire creative and regrettable behavior.
It also helps to separate short-term exceptions from long-term policy tuning. If the same business app keeps getting blocked across multiple teams, the answer is probably not to approve the same emergency request fifteen times. It is to review the policy and improve it.
Final Thoughts
Trying to disable McAfee Endpoint Security may sound like the fast route, but in most managed environments it is neither the safest nor the smartest option. The better strategy is to identify the exact block, work through approved channels, use temporary exceptions when justified, and keep the rest of the device protected.
That approach supports security, compliance, and common sense all at once. It may not feel as thrilling as slamming the off switch like an action hero in a movie, but it is much more likely to keep your system safe, your job easier, and your inbox free of messages with the phrase “urgent incident review.”
Experience-Based Insights: What This Feels Like in Real Life
Anyone who has worked in a managed IT environment knows the emotional arc of a blocked task. It usually starts with confidence. You download a vendor-approved tool, double-click the installer, and expect the next screen to ask where you want the files to go. Instead, nothing happens. Or a warning pops up. Or the file vanishes into quarantine like it entered a witness protection program. At that moment, the temptation to find a quick way around endpoint protection feels very real.
For employees, the experience can be frustrating because the security tool is visible but the full policy behind it is not. You know something is blocking progress, but you may not know whether the issue comes from reputation-based scanning, exploit prevention, firewall settings, device control, or a rule your company added years ago after an incident nobody wants to relive. That lack of context can make the software seem arbitrary even when the protection is working as designed.
Developers often feel this pain more sharply. Local build tools, scripting frameworks, unsigned test binaries, and package managers can look suspicious to aggressive security controls. A developer might spend half an hour assuming the code is broken when the real issue is that a background protection layer is intercepting behavior that resembles something risky. The smart teams learn to build a repeatable process: test in an approved sandbox, document the file paths involved, gather the alert details, and request a policy review with specifics instead of panic.
IT admins see the issue from the other side. They know users are trying to get real work done, but they also know how often “This is definitely safe” turns into “We may need to isolate three laptops and reset a few credentials.” That is why experienced admins prefer narrow exceptions, maintenance windows, and business justification over broad changes. It is not stubbornness. It is pattern recognition earned the hard way.
There is also a trust factor. In organizations where IT responds quickly and explains decisions clearly, users are much more willing to follow the safe path. In organizations where requests disappear into a black hole, people start looking for unofficial fixes. That is when risk increases. Good security operations are not just about blocking threats. They are about giving legitimate work a reliable route forward.
The most successful teams treat endpoint security as part of daily operations rather than an obstacle course. They document common exceptions, maintain current software catalogs, keep policies tuned, and give users a simple escalation path. Over time, the drama decreases. The security tool still blocks what it should block, but fewer people feel tempted to go searching for ways to turn it off in the first place. And honestly, that is the ideal ending: less chaos, fewer false alarms, and one less reason to mutter at your laptop before coffee.