Table of Contents >> Show >> Hide
- The “Awful Pics” Prank: A Mini Case Study in Scambaiting
- Why Scams Feel So Sticky (Even When They’re Obvious)
- Scambaiting: The Joy, the Risks, and the Reality Check
- The Smartest Way to Handle Scammers (Without Becoming Their Hobby)
- Common Scam Flavors (and the Tells They Can’t Hide)
- If You Already Interacted With a Scammer
- So… Should You Send Fake Pics to Scammers?
- Extra: of Experiences Related to “Guy Pranks Online Scammer…”
- Conclusion
There are two kinds of people when a scammer slides into your DMs: the ones who block instantly, and the ones who think,
“What if I turned this into performance art?” The internet, being the internet, has plenty of volunteers for Team Performance Art.
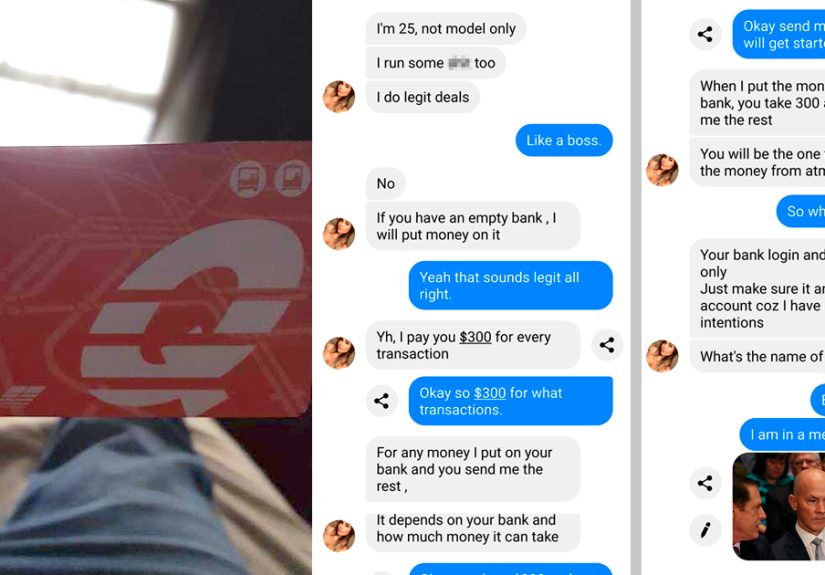
One viral scambaiting exchange captures that vibe perfectly: an online scammer tries to hustle a target into handing over sensitive info,
and the “target” replies with a parade of fake photos depicting increasingly awful (and increasingly absurd) misfortuneslike the universe
is personally speed-running a slapstick tragedy. The scammer keeps pushing. The guy keeps escalating. Comedy ensues.
But underneath the laughs is something real: scams are everywhere, and they work because they press the same human buttons over and overfear,
urgency, embarrassment, hope, and the desire to be helpful. So let’s enjoy the prank energy and talk about the smartest,
safest way to handle scammers in real life.
The “Awful Pics” Prank: A Mini Case Study in Scambaiting
The setup is familiar. A stranger appears online with a suspiciously urgent requestmoney, bank details, gift cards, a “verification code,”
access to an account, you name it. The pitch is usually wrapped in a story meant to short-circuit your common sense:
“I’m stuck,” “I’m in trouble,” “Your account will be closed,” “You won,” “This is the police,” etc.
In this prank version, instead of arguing or panicking, the guy responds like he’s living inside a cursed cartoon.
The scammer asks for something straightforward. The guy says he would help… but he’s currently dealing with a calamity.
Then comes the photo: an “accident,” a “disaster,” a “medical emergency,” or some other outrageous mishapclearly staged, clearly fake,
and clearly designed to waste time.
The funniest part is the rhythm. Scammers often follow a script. They’re trained to keep steering the conversation back to the payoff.
So the scammer tries to ignore the chaos and push forward. The guy answers with more chaos. It becomes a loop:
scam demand → tragic update → ridiculous photo → scam demand → even worse tragic update.
As a piece of internet theater, it’s satisfying. It flips the power dynamic. The scammernormally the one driving the interactiongets stuck
in the passenger seat of a bus headed to Nonsense Town.
Why Scams Feel So Sticky (Even When They’re Obvious)
If you’ve ever thought, “Who falls for this?”congrats, you’re human. Also: you’re not immune. Scams don’t succeed because victims are dumb.
They succeed because scammers are relentless, and the best cons don’t feel like cons at first.
1) Pressure and urgency
Scammers love clocksreal or imaginary. They’ll claim a deadline, a “final notice,” or a crisis that requires action right now.
Urgency is a classic way to stop people from verifying details.
2) Authority and impersonation
Many scams borrow credibility from institutions you’re trained to respect: government agencies, banks, delivery carriers,
tech companies, even your workplace. If the message “sounds official,” the scammer has already won half the battle.
3) Emotion: fear, hope, love, embarrassment
Fear gets clicks. Hope gets transfers. Romance gets long conversations. And embarrassmentespecially threats like
“We have compromising footage”gets people to do things they’d never do in daylight.
4) Familiar “payment rails” that are hard to reverse
Gift cards, wire transfers, crypto, “refund” schemesscammers prefer routes that are fast and difficult to trace or claw back.
If someone insists on one of these methods, it’s not “a preference.” It’s a red flag with headlights.
Scambaiting: The Joy, the Risks, and the Reality Check
Scambaiting (a.k.a. “messing with scammers”) has become its own corner of internet culture: prank texts, fake personas,
long-winded email sagas, even entire YouTube channels dedicated to wasting scammers’ time. The appeal is obvious:
it feels like a tiny act of justiceone less minute the scammer can spend targeting someone vulnerable.
But here’s the reality check: many consumer-protection and cybersecurity experts recommend not engaging.
Not because the scammer deserves peace and quiet, but because engagement can create new problems for you:
- You confirm you’re a real person. Replying can tell scammers your number/account is active, which may lead to more targeting.
- You increase your exposure. A back-and-forth can nudge you into clicking a link, opening a file, or sharing “just one detail.”
- You invite escalation. Some scammers retaliate with harassment, doxxing attempts, or flooding your inbox/phone.
- You can trip into legal/ethical mess. “Pranks” that involve threats, harassment, or sharing someone’s personal data can backfire.
The prank exchange is funny because it’s staged to be low-risk (fake pics, no sensitive info, no links clicked).
Real life is messier. If you’re going to “win,” the safest win is boring: don’t respond, block, report, and secure your accounts.
The Smartest Way to Handle Scammers (Without Becoming Their Hobby)
Step 1: Don’t click, don’t call, don’t reply
If a message is unexpected and tries to push you into action, treat it like a suspicious package:
don’t open it on your kitchen table. Verify through official channels you find yourself (not the contact info in the message).
Step 2: Screenshot, then block
If you want to report it, grab a screenshot (or keep the email header, if you know how). Then block the sender.
The goal is to keep evidence, not keep the conversation alive.
Step 3: Report it where it matters
Reporting feels like yelling into the voiduntil it doesn’t. Aggregated reports help agencies and platforms spot patterns, warn the public,
and sometimes build cases. In the U.S., common reporting routes include federal consumer-fraud reporting portals and cybercrime intake centers.
Step 4: Lock down your digital life
Use multi-factor authentication, unique passwords, and password managers. Keep devices updated. And be extra cautious with “verification codes”:
scammers love asking for codes because those codes can be the keys to your account.
Common Scam Flavors (and the Tells They Can’t Hide)
Imposter and government-themed scams
The tell: threats, urgency, and unusual payment requests. If someone claiming to be from a government agency demands gift cards,
wire transfers, or immediate payment to avoid arrest, that’s not how it works.
Tech support scams
The tell: unsolicited calls or scary pop-ups insisting your device is infected and you must grant remote access or pay for a “fix.”
Legitimate support doesn’t cold-call you out of nowhere to “save your computer.”
Phishing emails and “your account is locked” messages
The tell: links you didn’t request, pressure to “verify,” and subtle lookalike domains. Don’t use the linknavigate to the official site
yourself, or contact support through a number you already trust.
Smishing (SMS phishing) and delivery-tracking texts
The tell: a text claims a package can’t be delivered until you click a link or “confirm” info. Delivery-themed bait is popular because
it hits when people are already expecting shipments.
If You Already Interacted With a Scammer
First: don’t beat yourself up. These operations are designed to create panic and momentum. What matters is what you do next.
- Stop contact immediately. No “last message,” no “gotcha,” no closure.
- Secure accounts. Change passwords, enable multi-factor authentication, and review recent logins.
- Watch financials. Monitor bank/credit card activity and consider a fraud alert or credit freeze if sensitive info was shared.
- Report quickly. The faster you report, the better the chance of limiting damage and helping pattern detection.
So… Should You Send Fake Pics to Scammers?
As comedy, the “awful pics” prank is a chef’s kiss: low effort, high absurdity, maximum time-waste. As a life strategy, it’s a risk-reward question.
If you engage, you’re stepping onto a field the scammer plays on all day, every day.
If your goal is to protect yourself and the people you care about, the best move is usually not a prankit’s prevention:
teach the red flags, normalize verification, and make “I’m going to double-check” the default reaction to urgency.
Keep the prank energy for your group chat. Use the safety energy for your real accounts.
Extra: of Experiences Related to “Guy Pranks Online Scammer…”
Most people don’t remember the first scam message they ever gotbecause it didn’t feel historic. It felt like junk mail with a pulse.
A random text about a “package issue.” An email about a “password reset.” A social message from someone you don’t know saying,
“Hey, is this you in the video?” The hook is almost always ordinary enough to click when you’re tired, distracted, or mid-errand.
That’s why the “fake awful pics” prank resonates: it’s the fantasy response. Instead of being startled, you become the chaos.
Instead of being tested, you test the scammer’s patience. People who’ve been targeted describe a similar emotional arceven when they
don’t prank. First comes the micro-jolt of anxiety (“Wait… did I mess up?”). Then the second wave: irritation (“Seriously, again?”).
Then, if you’ve been hit repeatedly, a third feeling shows up: the urge to do something. Anything. Even if it’s just sending
the scammer a photo of a very dramatic, very fake disaster unfolding in your living room.
One common experience is the delivery-text spiral. You get a message claiming a carrier needs an address confirmation or a “small fee”
to release a package. If you replyeven with a snarky “nice try”the number suddenly feels busier. More texts arrive. Different numbers.
Same script. It’s like stepping on a rake and discovering the yard is made of rakes. The best lesson people report learning the hard way:
silence is a shield. Don’t feed the system your attention.
Another frequent story: the tech support scare. A pop-up flashes, alarms blare, and a number appears telling you to call immediately.
People describe the moment as oddly physicalheart rate up, palms sweaty, brain shouting, “Fix it now!” The scam works not because
the pop-up is convincing, but because urgency is contagious. Those who avoided harm usually did one simple thing: they paused,
closed the browser (or powered down), and asked someone else to look. That tiny delay breaks the spell.
Then there’s the “wrong number” opener that turns into a friendly chat. It can feel harmlessalmost charminguntil it isn’t.
The conversation shifts toward a “can’t-miss opportunity,” a link to a platform, or a request to move to another app.
People who recognized it early often say the same thing: the friendliness was too smooth, too fast, too agenda-shaped.
Real friendships don’t come with a conversion funnel.
So where does that leave the prank idea? For some, humor is how you reclaim controllike putting a clown nose on something that tried to scare you.
If you keep it as a private joke (“Look what they tried today”), it can be cathartic and even useful for education. The risky part is
turning the scammer into your scene partner. Because the moment you engage, you’re giving them a live wire: your time, your attention,
and a chance to pivot into a different angle.
The healthiest “scambait” most people can do is community-based: warn friends and family about the latest scripts, normalize verifying
requests through trusted channels, and share the rule that saves the most money: if someone is rushing you, that’s your cue to slow down.
You don’t need fake disaster pics to beat a scam. You need a pause buttonand permission to use it.